Every few months, we send out a newsletter to all Gruntwork customers that describes all the updates we’ve made since the last newsletter and news from the DevOps industry. Note that some of the links below may go to private repositories in the Gruntwork Infrastructure as Code Library that are only accessible to customers.
As always, if you have any questions or need help, email us at support@gruntwork.io!
Gruntwork Updates
The Cliff Notes
- Gruntwork Pipelines adds support for self-hosted partially air gapped Github Enterprise and Gitlab instances
- Gruntwork Pipelines Ignore list now passes down to Terragrunt excludes
- Control Tower module hits 1.0 with the release of an async multi-account-factory module
- VPCv2 nearing completion
- SemVer migration over halfway complete
Gruntwork Pipelines Self Hosted
We're excited to announce that Gruntwork Pipelines now supports self-hosted, partially air gapped GitHub Enterprise and GitLab instances. This enhancement allows organizations with strict security requirements to leverage the power of Gruntwork Pipelines while maintaining their isolated infrastructure environments.
Gruntwork Pipelines now works in environments with no inbound internet connectivity while still maintaining best practices for role assumption via OIDC. No hard coding long lived credentials.
This update ensures that enterprises with the most stringent security requirements can adopt Gruntwork Pipelines without compromising their security posture or existing infrastructure constraints.
Gruntwork Pipelines Ignore List
We recently shipped a feature to Gruntwork Pipelines that will generate and consume a .terragrunt-excludes file to Terragrunt based on the configured Pipelines exclude. Our original design let Pipelines ignore certain file changes for the purposes of adding them to the run queue but those units may show up in the DAG anyway if included from somewhere else. The thought was to allow end users the flexibility to control the specific behavior of how the run queue was executed.
In customer interviews, we found that consumers wanted Gruntwork Pipelines to act more as a transparent extension to Terragrunt and not as a separate tool to configure. Separate ignore lists were confusing so we collapsed down to one.
Check out the full docs for the ignore-list here.
Control Tower
- New modules
control-tower-account-factory-async,control-tower-multi-account-factory-asyncandcontrol-tower-provisioned-product-artifact-updater- The standard synchronous approach to provisioning or updating AWS accounts via Control Tower can lead to lengthy OpenTofu/Terraform runs, especially when Control Tower APIs are slow or when updating a large number of accounts. More importantly, certain types of "drift" caused by Control Tower changes are difficult to reconcile using OpenTofu/Terraform alone.
- These new module implement an asynchronous approach by deploying infrastructure (EventBridge, SQS, Lambda, and AWS Step Functions) that monitors for certain API calls. When relevant API calls are made (
UpdateProvisioningArtifactandUpgradeProduct), the Lambda is triggered to complete the update process independently of OpenTofu/Terraform.
VPC v2
Our full VPC rework is nearing completion. We've taken customer feedback and created a set of modules flexible enough to shape into extremely esoteric use cases while still providing our baseline vpc-app 5 tier architecture.
Please take a look at the branch and let us know what you think.
SemVer Migration
Nearly 2/3's of our module repos have officially been tagged up to 1.0.0 or above. We have 8 holdouts left and are actively working on shaking loose any deprecations before adopting the SemVer promise with them. Our most commonly used modules that customers have asked for the most have been upgraded first.
Your voice shapes our roadmap. If you'd like your modules prioritized next, please let us know.
Terragrunt Updates
Introduction of the runner-pool experiment
New runner-pool experiment to improve the performance of the Terragrunt concurrency model.
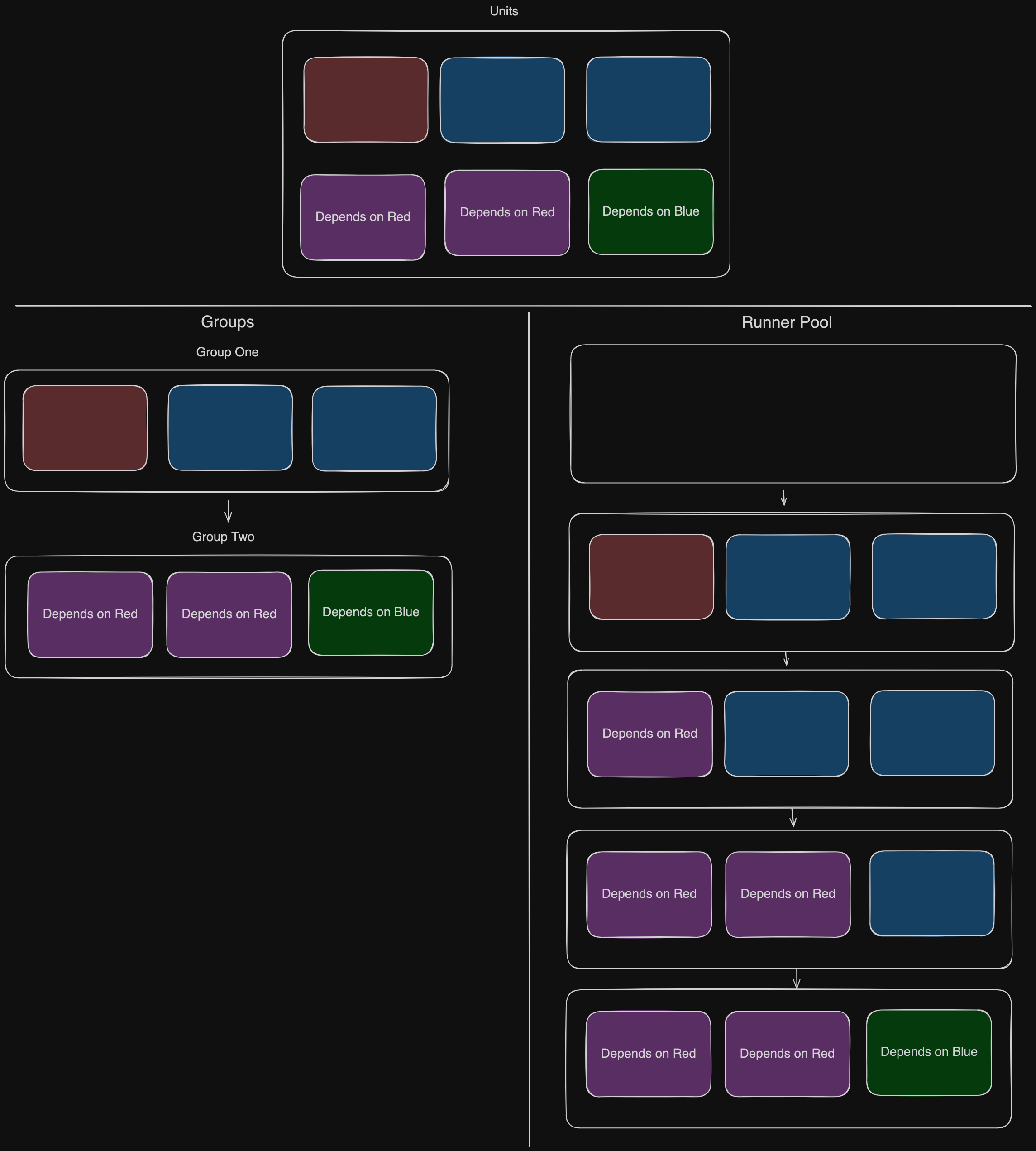
This experiment will be generally available once RFC #3629 is complete, improving the performance of Terragrunt runs within stacks.
Support for OpenTofu 1.10 Native S3 Locking
The remote_state S3 backend now integrates natively with the OpenTofu 1.10 feature of state locking via S3 without the usage of DynamoDB using the new use_lockfile attribute.
# Configure OpenTofu/Terraform state to be stored in S3 with native S3 locking instead of DynamoDB.
# This uses S3 object conditional writes for state locking, which requires OpenTofu >= 1.10.
remote_state {
backend = "s3"
config = {
bucket = "my-tofu-state"
key = "${path_relative_to_include()}/tofu.tfstate"
region = "us-east-1"
encrypt = true
use_lockfile = true
}
}In previous releases, if users wanted to integrate with this OpenTofu feature, they would have to use the generate attribute, which opts users out of more advanced features of Terragrunt remote state management like automatic provisioning of state resources.
By using the native attribute in config, users can retain the benefits of automatic backend bootstrapping in addition to native integration with the new OpenTofu feature.
You can learn more about backend configurations in the HCL docs.
Introduction of the auto-provider-cache-dir experiment
The new auto-provider-cache-dir experiment has been added to automatically configure OpenTofu provider caching when certain conditions are met:
- You are using OpenTofu
- You are using a version of OpenTofu >= 1.10
This leverages recent improvements in how OpenTofu handles provider caching to allow for safe concurrent access to provider plugins in OpenTofu 1.10.
In micro-benchmarks, the native provider cache directory out-performs the Provider Cache Server, as the overhead of starting and running the provider cache server is eliminated.
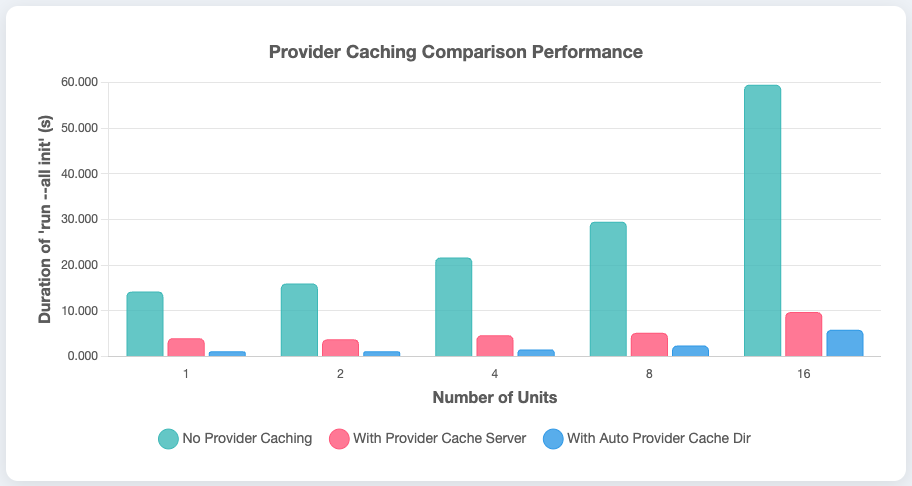
Once generally available, this feature will be enabled by default, automatically providing performance improvements to Terragrunt users using OpenTofu >= 1.10. If you are currently using the Provider Cache Server, you are advised to experiment with this feature, and share your feedback.
You can learn more about the feature in the dedicated feature docs, including a comparison with the Provider Cache Server, so you can learn if limitations in how the native OpenTofu provider cache directory works will result in a requirement to continue using the Provider Cache Server going forward.
Special thanks to @cam72cam for coordinating with us to get this long-awaited feature supported in OpenTofu to meet the needs of the IaC community.
The cas experiment now supports terraform block source attributes
The cas experiment now supports de-duplication of OpenTofu/Terraform module source cloning during unit initialization.
This both reduces time spent cloning OpenTofu/Terraform module sources by reducing network bandwidth overhead, and reduces disk utilization.
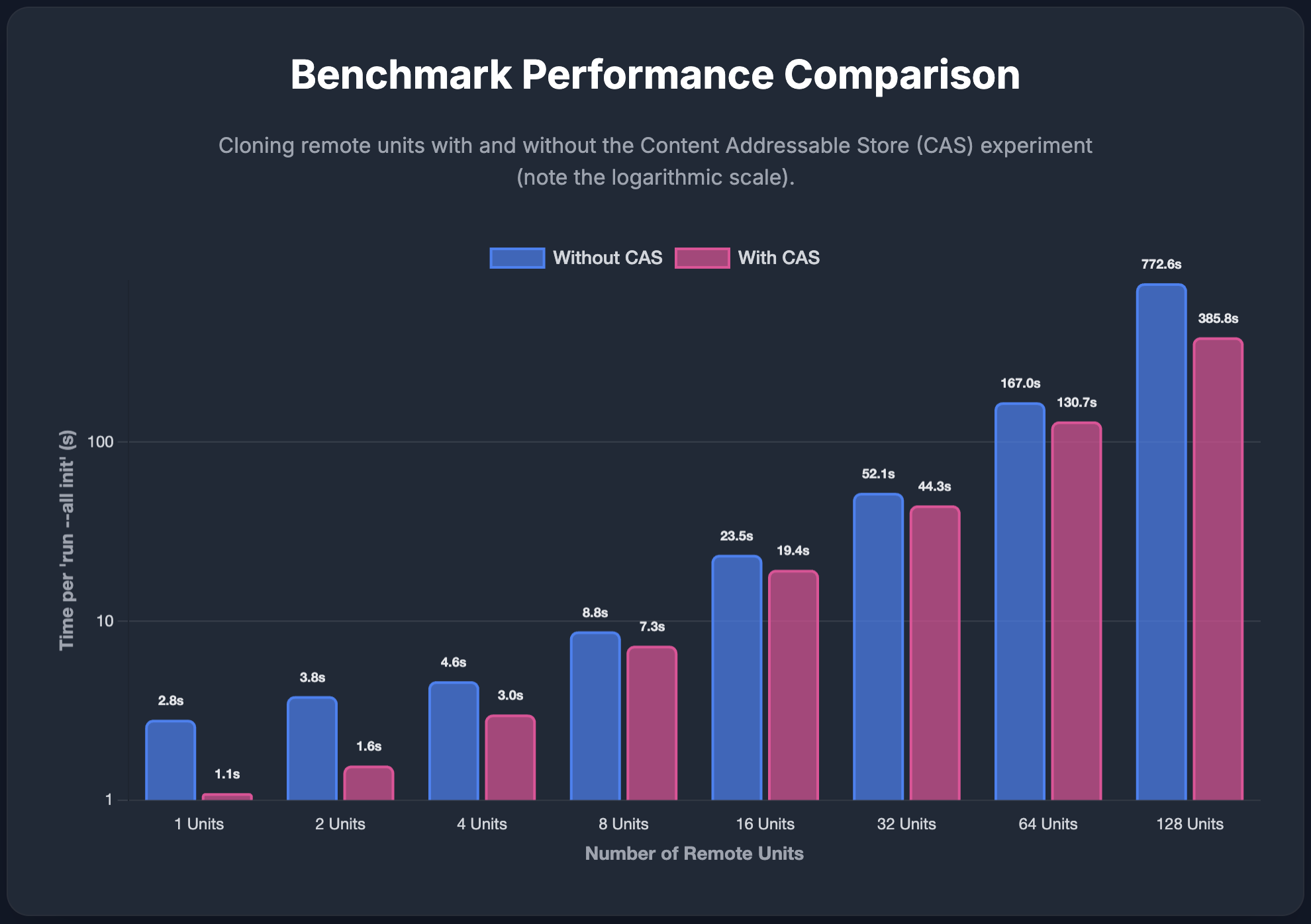
You can learn more about the CAS feature in the dedicated feature documentation.
Styling for Run Summary Updated
Per design feedback, the styling for Run Summaries has been updated slightly.
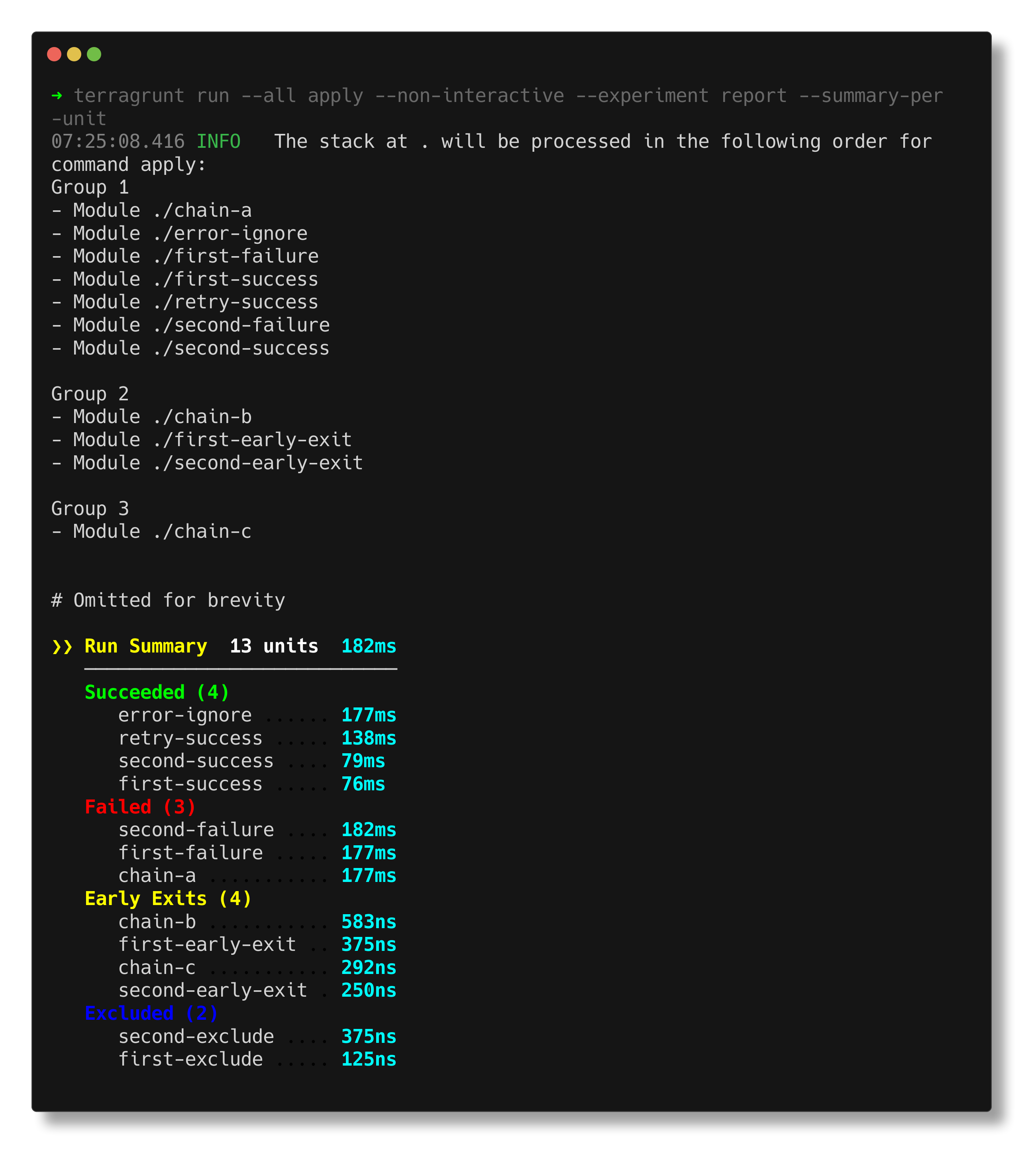
The report feature is now considered feature complete. Any further updates will be made to address community feedback.
Scaffold now supports Boilerplate dependencies and partials
The Scaffold feature now supports leveraging Boilerplate dependencies and partials.
This was a missing feature in the integration between Scaffold and Boilerplate, and Terragrunt users do not have to change anything in how they invoke Scaffold to have custom Boilerplate templates properly render using those Boilerplate features.
Special thanks to @tgeijg for contributing this feature!
Terragrunt now supports using credentials in .terraformrc files
Terragrunt now supports credentials stored in .terraformrc files when fetching from private registries, in addition to the fallback mechanism of using TG_TF_REGISTRY_TOKEN.
Special thanks to @dlundgren for contributing this feature!



- No-nonsense DevOps insights
- Expert guidance
- Latest trends on IaC, automation, and DevOps
- Real-world best practices